Windows VPN RRAS SSTP static routing to client
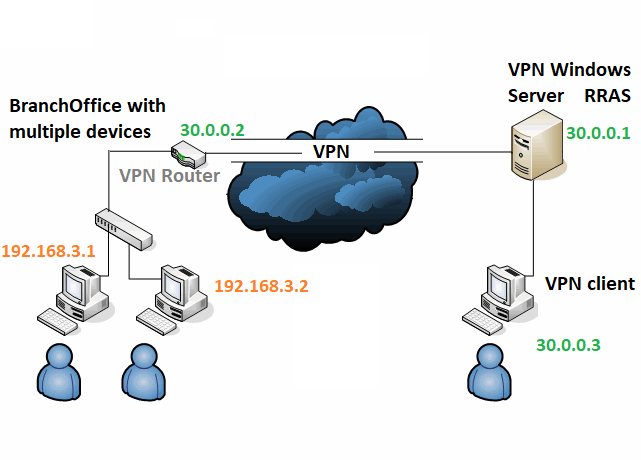
When you want to connect a BranchOffice to your VPN, you can configure a VPN client on every client, or you make use of a Server or VPN router to do it centrally. (we use for example the RUT240 because it supports SSTP VPN)
When you create a VPN account and use it for this server or VPN router, you might discover that you are not able to connect back to devices connected to the local LAN of this server or router. if you try to ping, you get a “general failure”. googleing around will learn that you can either add a static route in CMD via add route, or even better, you can specify a static route on the user used for the VPN connection:
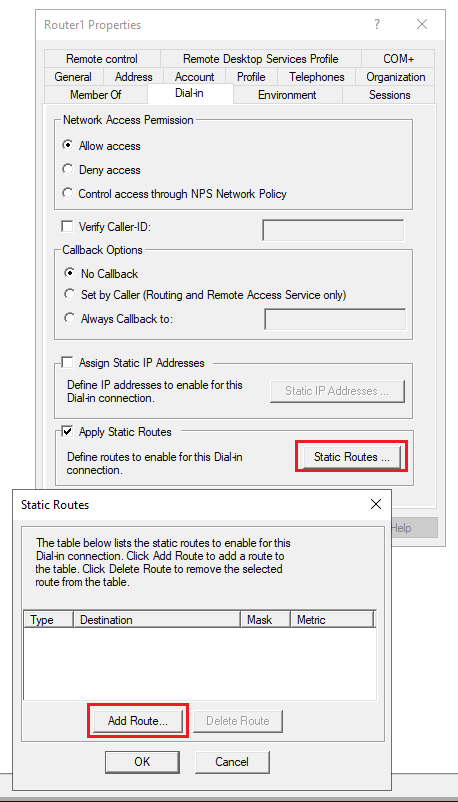
What a disappointment to discover that this static route does not work, or sometimes it works only the first time you applied it, but after a reconnection it is not working anymore. Although you clearly see the static route in CMD with Route Print.
Lucky you, it turns out to be possible. RRAS does mean Remote Routing Access Server for a reason. 🙂
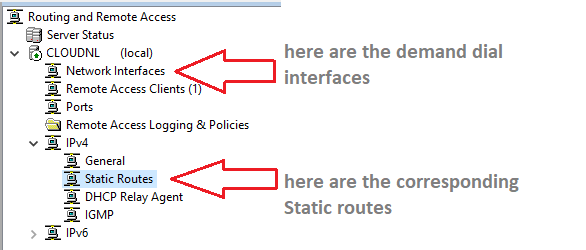
Go to RRAS:
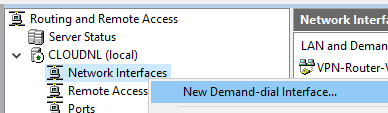
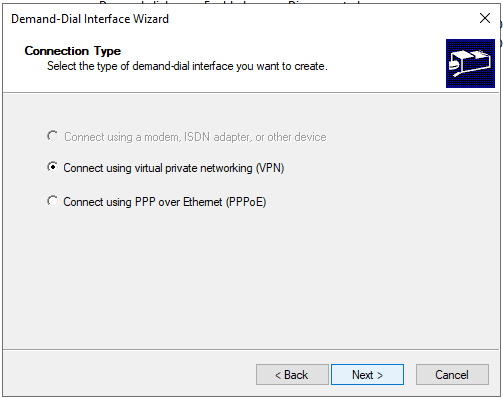
Add a Demand-Dial interface (right click Network Interface and select new Demand Dial Interface):
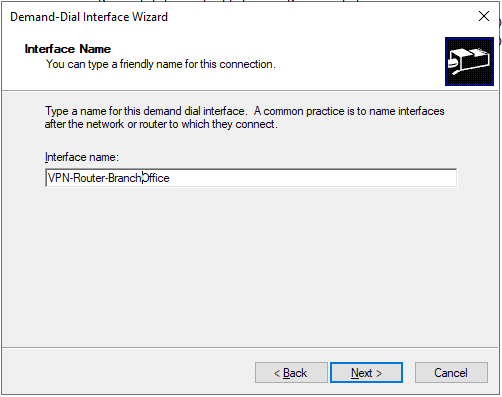
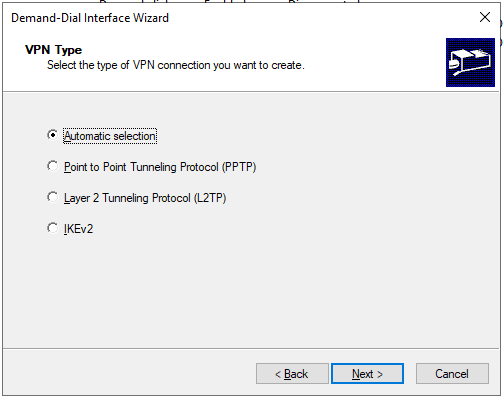
Pick a logical name, this name will be the name of the Demand Dial Interface and also be the name of the VPN user.
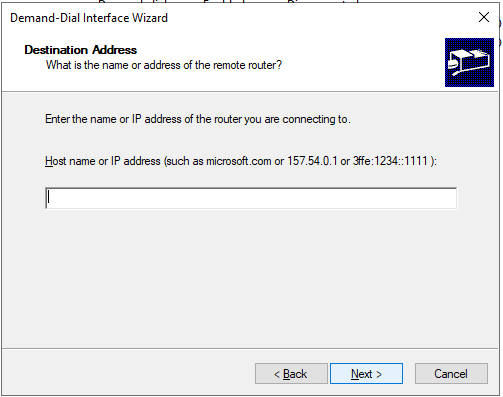
and here comes the solution: a Demand Dial interface is used for a Site-to-Site VPN connection, and you can configure the interface to automatically connect to the BranchOffice. (Then your branch office needs to have a fixed ipaddress, open port, RRAS running, etc.) In our case we don’t have that, and we don’t want to, we want the branchOffice to connect to the VPN server. So leave it empty(!).
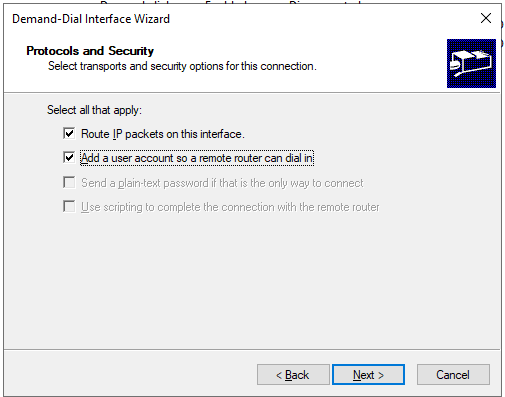
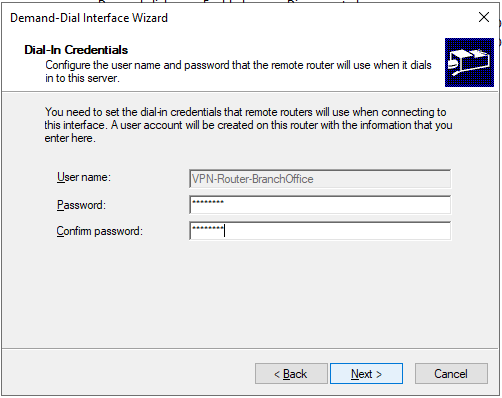
check “add a user account” this will create a user for your router to connect.
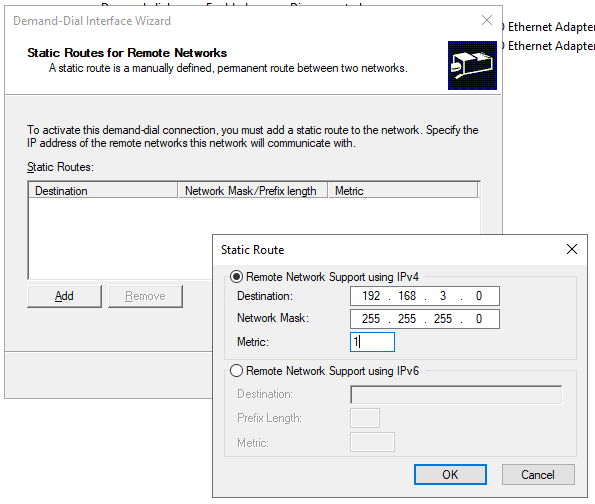
and now, add your static route here. in our example we want all traffic to 192.168.3.0 to be route through this interface to the Branchoffice.
Configure a password for this interface & user, so your Router/Server can connect to the server.
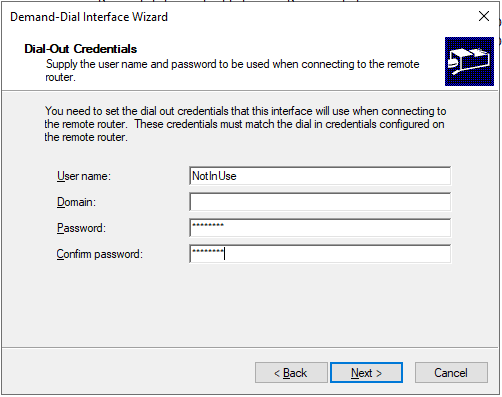
we don’t want this interface to connect anywhere, so just insert something to be able to proceed.
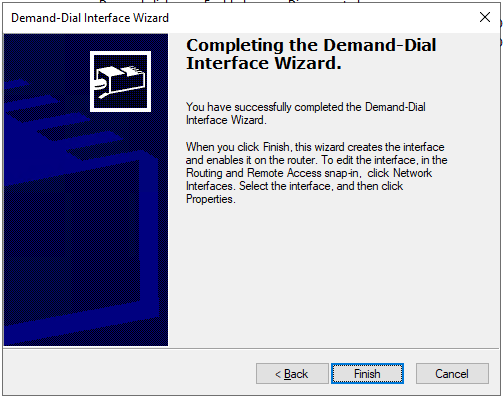
finished. Now configure your SSTP/IPSEC client (on your server or VPN Router) to use this Username and password to connect. Now RRAS will see this connection as a site-to-site VPN, and now you are able to ping from client 30.0.0.3 to client 192.168.3.2 in the BranchOffice.




Recente reacties